January 2009 Threatscape: Keylogging and spam problems, surge in exploit activity
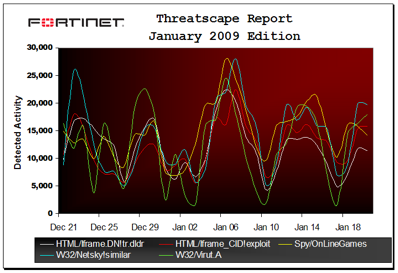
Fortinet announced its January 2009 Threatscape report revealed a surge in exploit activity. The headline-making buffer overflow exploit to Microsoft Security Bulletin MS08-067, which was originally detected in October ’08, continued to wreak havoc on un-patched machines during the end of December ’08 and throughout January ’09, landing in ninth position in this period’s Top 10 Exploitations list. The highest recorded activity for this exploit occurred on January 14 and overall new vulnerabilities rose four percent since last period.

Also climbing the ranks, online gaming malware continued to build on December’s momentum with two Trojans increasing in activity. Spy/OnLineGames claimed first place on Fortinet’s Top 100 malware variants list while, not far behind, W32/Dropper.VEM!tr jumped 94 spots, further highlighting a rising wave of online gaming malware designed to pilfer credentials.
Fortinet’s FortiGuard Global Security Research team also observed a mounting trend in spam, which drew from ongoing economic concerns and leveraged the Presidential Inauguration as part of a social engineering campaign.
Following are key findings from Fortinet’s January 2009 Threatscape report:
- Exploits/Intrusion – 43 new vulnerabilities were added to the FortiGuard IPS coverage this period, with 13 reported to be actively exploited; the number of active exploits for new vulnerabilities rose to 30.2 percent this period, up from 26.2 percent last period;
- Malware – keylogging and information siphoning obtained the majority of activity reported during this period, with online gaming exploits rising up the charts; the U.S. (45.05%) and Japan (43.03%) were still the most targeted regions for malware, with China (26.77%), Taiwan (20.61%) and India (20.54%) grabbing up the 3rd, 4th and 5th positions as the top most targeted regions;
- Spam – spam rates continued to increase this period and fully regained levels consistent to spam rates before the McColo take-down; driven by the financial crisis, the most popular spam campaigns included positive salary structure, diploma and education schemes and added scam tactics seeding a new botnet that centered on President Barack Obama’s inauguration;
- Web traffic – Web activity blocked during this period stayed in close alignment to last month’s findings, with pornography maintaining the top spot at almost 70 percent; malware also consistent at nearly 20 percent and spyware and phishing activities representing the remaining 10 percent.