Multi-target phishing campaign hits webmail users
An active phishing campaign that is simultaneously targeting Gmail, Yahoo, AOL and Windows Hotmail email users has been spotted by Webroot.
The potential victims receive a bogus “Internet Server Service Alert” seemingly coming from their email provider, with an offer to secure their mailbox from spamming mailing lists that seems just a click on a link away.
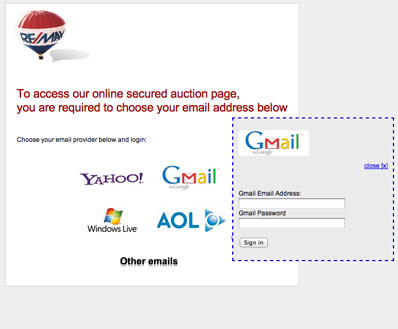
Bizarrely enough, the page on which they land bears a logo of a real estate company and offers access to a secured auction page:
Now, where have I seen this already?
As it turns out, the page is an exact copy of one used in another phishing campaign spotted in May, when the spammy email and phishing page actually pushed the same agenda, and were trying to take advantage of the users’ vague familiarity with the OpenID authentication method.
As it was then, the current phishing is hosted on a compromised legitimate site, which is currently detected by all 28 phishing URL scanning services used by the VirusTotal service as a “clean site.”
“Cybercriminals are masters of multi-tasking,” comments Webroot’s Dancho Danchev. “For instance, whenever a web server gets compromised, they will not only use its clean IP reputation to host phishing, spam and malware samples on it, they will also sell access to the shell allowing other cybercriminals the opportunity to engage in related malicious activities such as, mass scanning of remotely exploitable web application vulnerabilities.”