Hidden crypto currency-mining code spotted in apps on Google Play
You already know that cyber criminals are using malware to make victims’ computers mine crypto currencies for them, but did you know that your phone can be instructed to do the same?
A month ago researchers from G Data discovered mining code hidden in several repackaged popular Android apps on 3rd party apps stores. Lookout researchers are now warning of similar apps being offered on Spanish forums dedicated to the distribution of pirated software, and made for mining Bitcoin, Litecoin, and Dogecoin.
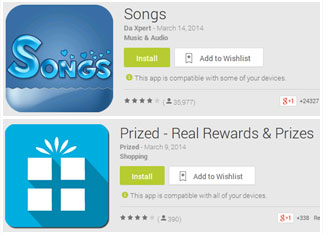
And, finally, Trend Micro researchers have discovered two apps – a song manager and shopping app – that have the mining code added to them and are (still!) being offered for download on Google Play:
In the case of the apps found by G Data researchers, they contained CPU mining code from a legitimate Android cryptocurrency mining app. The mining would start once the miner detected that the affected device is connected to the Internet.
The aforementioned two apps found in the Google Play store have been downloaded at least a million of times, and likely even more.
“Analyzing the code of these apps reveal the cryptocurrency mining code inside. Unlike the other malicious apps, in these cases the mining only occurs when the device is charging, as the increased energy usage won’t be noticed as much,” the researchers noted.
They also pointed out that “reading their app description and terms and conditions on the websites of these apps, users may not know that their devices may potentially be used as mining devices due to the murky language and vague terminology.”
The apps are still offered for download, but according to Malwarebytes’ Armando Orozco, the developer of the Songs app has removed the mining code since it was first spotted and its existence made public by Trend Micro.
“Although they’re removed the code, I would not trust this app or developer. They could easily update again reintroducing the code,” Orozco pointed out.
While some of the criminals might earn themselves some crypto currency this way – especially if they concentrate on mining lesser known types – the question is whether they can have much success in the long run.
“Phones do not have sufficient performance to serve as effective miners,” the researchers explain. Users will also quickly notice the odd behavior of the miners – slow charging and excessively hot phones will all be seen, making the miner’s presence not particularly stealthy. Yes, they can gain money this way, but at a glacial pace.”