New Android Trojan downloaded from Google Play by millions
Millions of Android users have been tricked into downloading a new Trojan masquerading a slew or legitimate apps directly from Google Play, warns Lookout researcher Marc Rogers.
The newly discovered malware family has been dubbed BadNews, and it’s capable of harvesting and sending information about the device to its C&C server, send out fake news messages, and prompt users to install additional malicious applications such as the AlphaSMS premium rate SMS Trojan.
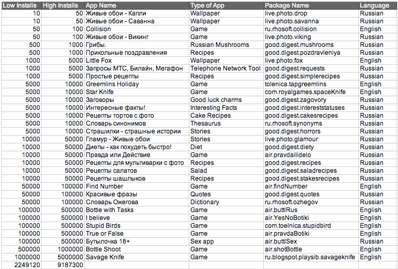
BadNews was packaged with games, wallpaper apps, dictionary and dieting apps, and many others, the majority of which were obviously aimed at Russian-speaking users (click on the screenshot to enlarge it):
“It is not clear whether some or all of these apps were launched with the explicit intent of hosting BadNews or whether legitimate developers were duped into installing a malicious advertising network,” says Rogers. “However, based on our analysis of the backend code behind a number of these purported ad networks there is little doubt that BadNews is a fraudulent monetization software development kit.”
32 apps have been found containing the malware, and they were offered to users via four distinct developer accounts. The apps have by now been removed, and the accounts closed by Google. Still, between two and nine million users have downloaded one or more of them until that move, say Google Play statistics.
But how is it possible that these trojanized apps went undetected by Google long enough to do such damage?
Well, it’s because it didn’t act immediately. It used a server to delay its behavior, tricking the vetting process and Google’s Bouncer into thinking the app in question wasn’t malicious.
Once installed on a device, BadNews would trick users into permitting the installation of additional SMS toll fraud apps by offering them as “critical updates” for Vkontakte and Skype.