Employees targeted with faked emails from payroll services firms
Administrators at companies that outsourced payroll management to outside firms have recently been heavily targeted with malicious emails supposedly coming from those very same companies, warn SANS ISC researchers.
“For the past couple of weeks, companies that offer outsourced payroll management services have seen their name being abused for phishing scams. One prominent example is ADP, whose website currently alerts their customers to four different samples of phishing emails that make the rounds and claim to be from ADP,” Daniel Wesemann writes.
The subject and the text included in the emails in question makes them especially dangerous to HR/payroll employees who actually use ADP services, as reading that their access to ADP is about to be cut off due to the expiration of a digital signature is likely to make them panic and follow the offered link:
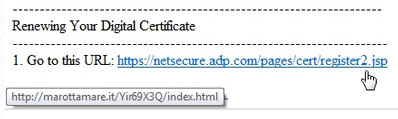
As you can see, the link is not what it claims to be. Through a number of redirections, the victims are taken to a website serving a number of exploits, and among them is the currently very popular exploit for the Java CVE2012-1723 flaw.
This particular exploit is still detected only by a handful of AV solutions, and that’s probably because the original attack code and payload are split up into five byte blocks and encoded separately by XOR with a different static value, Wesemann speculates.
The malware that is ultimately delivered onto the victims’ computer is likely a keylogger or an information-stealing Trojan.
“Few things are as juicy for the bad guys as getting a key-logger onto the computer of someone who manages payroll,” Wesemann points out. “HR/payroll employees tend to have access to personal data of staff and usually have some form of access to a well-stocked bank account that is used to pay the wages.”
He advises companies to make sure that the Java hole in question is patched, that the aforementioned employees are again put through training that will allow them to spot phishing attempts such as these, and to make them carefully check out email logs for messages coming from the outsourced payroll provider in order to spot emails that say they are but they don’t.