iPhone secure messaging with self-destruct mechanism via Wickr app
![]() Wickr was one of the most interesting companies I was introduced to at this year’s RSA Conference in San Francisco. The company was one of the finalists of the Innovation Sandbox, a program that encourages out of the box ideas and the exploration of new technologies that have the potential to transform the information security industry. Wickr is a free app designed to provide private communication over a range of devices running Android and iOS.
Wickr was one of the most interesting companies I was introduced to at this year’s RSA Conference in San Francisco. The company was one of the finalists of the Innovation Sandbox, a program that encourages out of the box ideas and the exploration of new technologies that have the potential to transform the information security industry. Wickr is a free app designed to provide private communication over a range of devices running Android and iOS.
From a technical point of view, Wickr uses AES256 for encryption and ECDH521 for the key exchange. SHA256 is used for hashing and Transport Layer Security (TLS). All the encryption keys are used only once, and the Wickr servers don’t store any decryption keys. Besides the tough crypto, the key functionality of the service is the usage of a self-destruction mechanism for messages. Sounds quite good, especially with the recent snooping controversies.
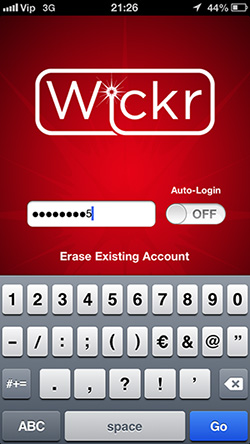
iPhone users can download the application from the App Store. Upon installation, there is a simple process of setting up an account. The application will ask you for the permission to access your contacts, which you can deny and add the contacts manually.
By default, messages in a discussion are sent with a self-destruction period of 5 days. The time period can be easily customised.

After the self-destruct time frame for a messages passes by, the message in question gets deleted and it’s gone forever since Wickr servers don’t store any messages. From a security standpoint, the system is very robust. You cannot even request a password reset – this function was deliberately skipped.

Besides textual communication, Wickr can be used for transferring videos, file attachments (via Box, Dropbox and Google Drive) as well as audio recordings.

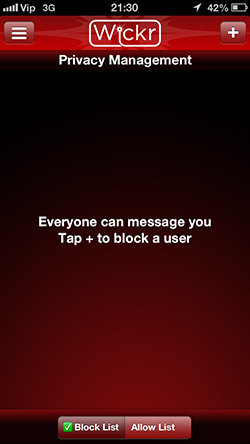
You can change the privacy settings of your Wickr account by setting up white or black lists for specific contacts you would like to allow or block.
Wickr is closed source which could raise some eyebrows. The company is co-founded by Nico Sell, a long time organizer of Def Con and Black Hat events, which definitely gives some credit to it. Famed security researcher Dan Kaminsky served as an advisor to the company and complimented the crypto efforts.
The solution is primarily aimed towards people that want to ensure their privacy, and don’t want someone to harvest their communication. The business model behind Wickr is still not absolutely clear, but according to a CNN report, the company will eventually charge its power users for in-app purchases, such as paying for a message to live forever.